Clock icon 7 minutes
The Behave Hub
The only cybersecurity awareness resources steeped in behavioral science and a wry sense of humor. Explore blogs, podcasts, e-books, webinars, and more—with a focus on what we do best—helping you manage and reduce your human cyber risk.
Do one more thing right today. Subscribe to the Behave newsletter

Filter results by
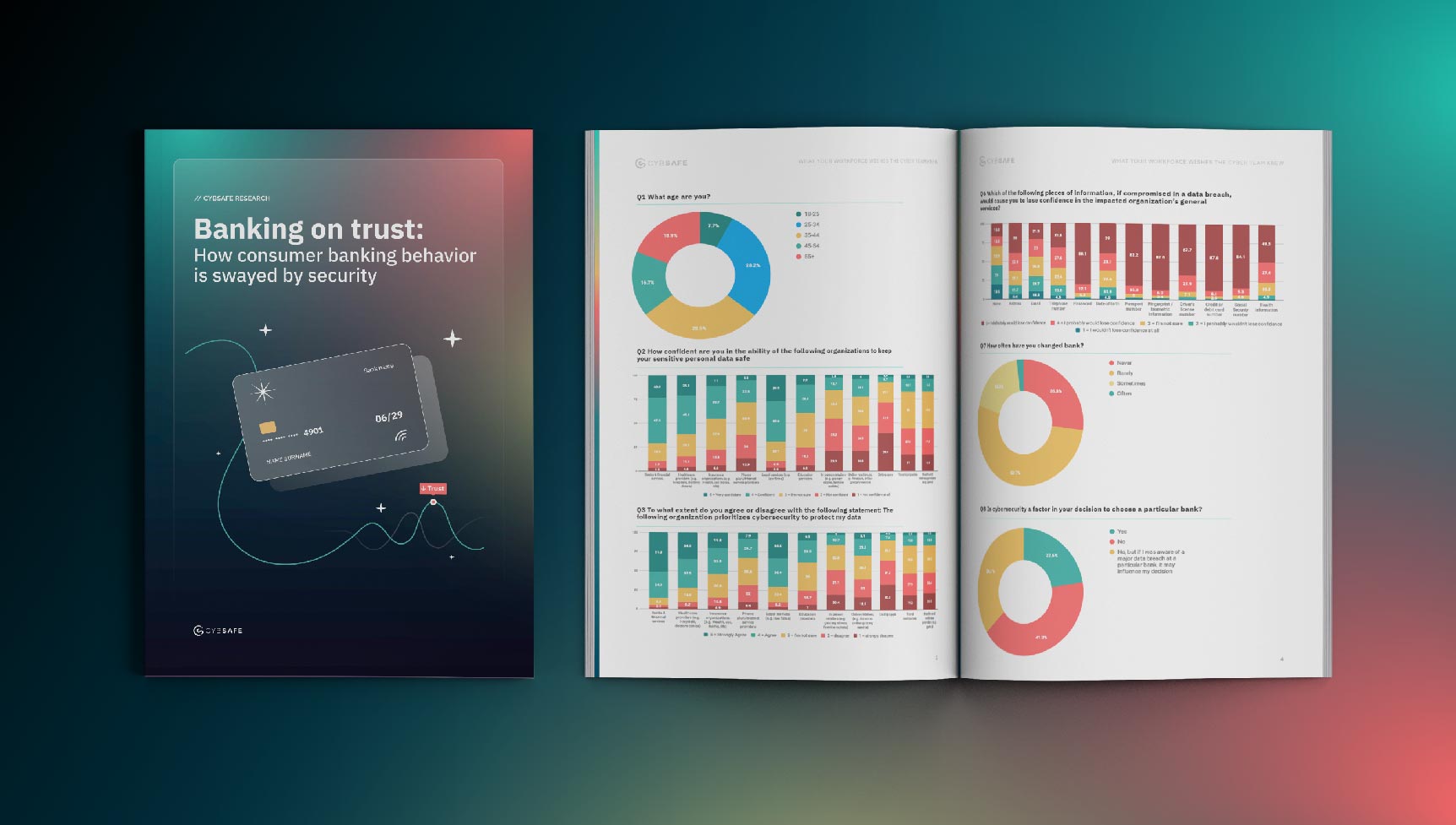
Other Resources
The world’s most comprehensive security behaviors database. Yours to explore.
A deep dive into the human element in cybersecurity. Read something revolutionary.
Everything we’re doing online or in person. Meet us there.
The Behave podcast—where your peers go to be heard. Spark new ideas.